I Spoke With ByteToBreach: The CAC Breach, Sterling Bank's €250,000 Ransom, and Why Nigeria
The threat actor behind Nigeria's biggest breach series answered my questions.
More than a week ago, I published an investigation into the Sterling Bank and Remita breaches. The Nigeria Data Protection Commission had just opened investigations. National outlets covered it. The story travelled further than anything Web Security Lab had previously published.
Then ByteToBreach hit the Corporate Affairs Commission.
I decided to ask him directly.
On April 15 at 5:03am, I sent 10 questions to the contact address the threat actor had published in their own forum post.
The questions covered Sterling Bank, Remita, the CAC, the human consequences, data modification and whether they had contacted any of the affected organisations before dumping their data.
He responded.
The same day the Corporate Affairs Commission issued its first public statement on the breach.
Two institutions — one criminal, one governmental — both going on the record on April 15.
This is what they said, what it means, and what it reveals about the third Nigerian institution in his campaign so far.
The Pattern
There is a rhythm to how ByteToBreach operates in Nigeria.
They find a door. They walk through it. They document everything they find inside with the methodical patience of someone who knows they will not be interrupted. Then they post about it.
The first door was a pilot server at Sterling Bank, an unpatched vulnerability on a testing environment that nobody was watching closely enough.
The second door was Remita’s Git repository, unlocked with credentials sitting in plaintext inside production configuration files. Nine days at Sterling Bank. Fourteen days between Remita and publication.
Nigeria’s financial infrastructure was documented and published on criminal forums while the institutions affected said nothing to their customers.
The third door was different.
Not because the vulnerability was more sophisticated, it was, if anything, simpler than anything that came before it.
Not because the data was more sensitive, though it is, in ways that will take time to fully reckon with. But because this time the actor did not just find a door into a database.
They found a door into a registry. And registries are not read-only.
What the CAC Actually Is
Most Nigerians know the Corporate Affairs Commission as the place you go when you need to register a company. Pay the fees. Submit the forms. Get your RC number. Move on.
That description is accurate as far as it goes. It does not go nearly far enough.
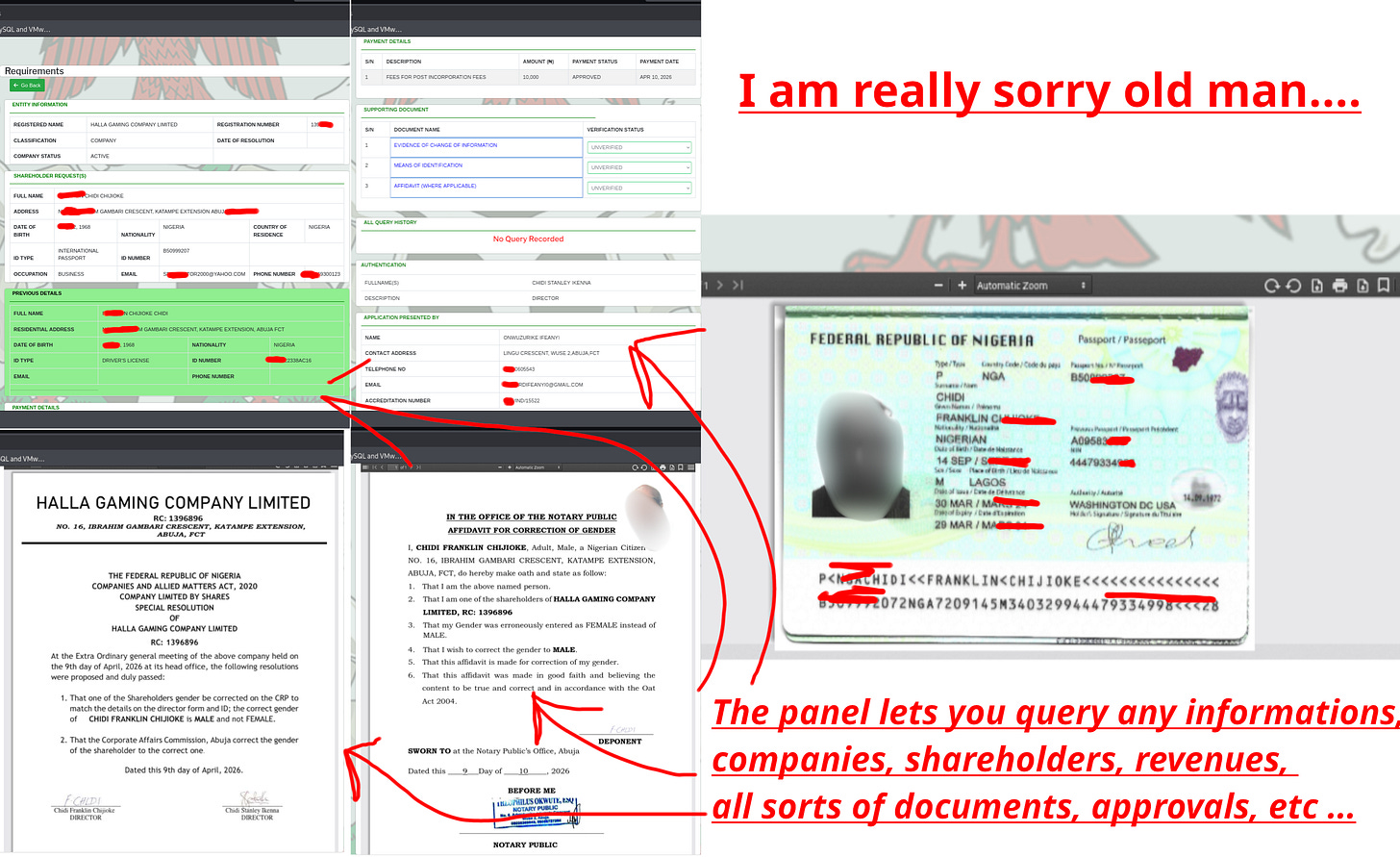
The CAC is the authoritative legal record of every company, business name, and incorporated trustee in Nigeria. Every director. Every shareholder. Every registered address. Every change of ownership. Every board resolution. Every piece of identity documentation submitted to verify that the people behind a company are who they say they are.
When a bank conducts due diligence on a corporate client, they check the CAC. When a court needs to establish the legal ownership of a company, it goes to the CAC. When the EFCC investigates a fraud, it pulls CAC records. When a contract is disputed, and the question is who actually controls an entity, the answer lives at the CAC.
This is not a commercial database that holds transaction records or payment histories. It is foundational infrastructure, the ground truth of Nigerian corporate identity. If the information in it is wrong, every system that depends on it is compromised.
That is the institution ByteToBreach walked into on or around April 10, 2026.
How He Got In
To understand how ByteToBreach got into the CAC’s administrative system, you need to understand one specific technical failure, one that the actor themselves described precisely in the artefacts they published.
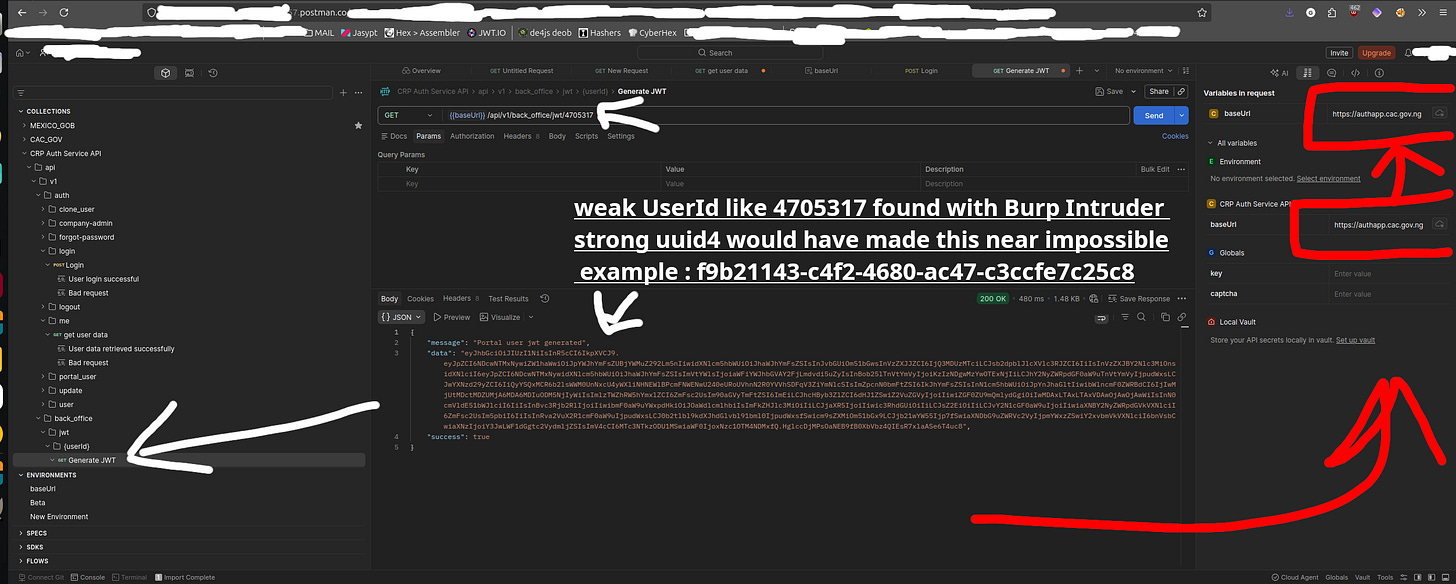
The CAC’s authentication infrastructure is built around a service called the CRP Auth Service API, hosted at authapp.cac.gov.ng.
This service handles login and session management for the CAC’s back-office portal, the administrative interface used by CAC staff to manage company registrations, process applications, and access corporate records.
When a user needs to access the back-office system, the service generates a JWT, a JSON Web Token, a digitally signed credential that says, in effect, “this person is authenticated and here is what they are allowed to do.” The endpoint that generated these tokens was at /api/v1/back_office/jwt/{userId}.
The problem was in that last part. {userId}.
In a properly designed system, user IDs are random, unpredictable strings, the kind of thing that cannot be guessed or enumerated.
The CAC’s system used sequential integers. User 4705310. User 4705311. User 4705312. A predictable, countable series that any attacker with basic tooling could walk through systematically.
ByteToBreach used Burp Suite, a standard security testing tool, to do exactly that. They sent requests to the JWT generation endpoint with incrementing integers until they found a valid user ID. The number they landed on was 4705317. The system returned a valid JWT token. No password. No second factor. No challenge. Just an integer and a token.
The actor’s own annotation on the screenshot is precise: “weak UserId like 4705317 found with Burp Intruder. strong uuid4 would have made this near impossible.”
They are correct. A UUID4, a randomly generated identifier with 2¹²² possible values, would have made this attack computationally infeasible. The CAC used sequential integers instead.
With the token in hand, the actor validated it against /api/v1/auth/me, which returned the full profile of the user whose ID they had obtained. Name: Ibrahim ****** . Email: i*******@cac.gov.ng. Phone: +23480360*****. Creation date: July 6, 2025.
An innocent CAC staff member’s credentials had just become ByteToBreach’s entry point into Nigeria’s corporate registry.
But when I asked ByteToBreach about the vulnerability class, he revealed something the artefacts alone had not shown.
“There weren’t any vulnerabilities, but a simple API exposure and misconfig. In the end, I realised you could download the files directly and without even going through the website. You can download directly from the subdomain edmsapp.cac.gov.ng, although it’s impossible to just guess the name of the files.”
There was a second access path entirely. Beyond the authenticated backoffice portal, the CAC’s document management system at edmsapp.cac.gov.ng permitted direct file downloads without any authentication, requiring only knowledge of the filename. No login. No token. No credentials. The barrier was not a lock. It was obscurity. If you knew what a CAC application file was named, you could download it directly from a public-facing subdomain.
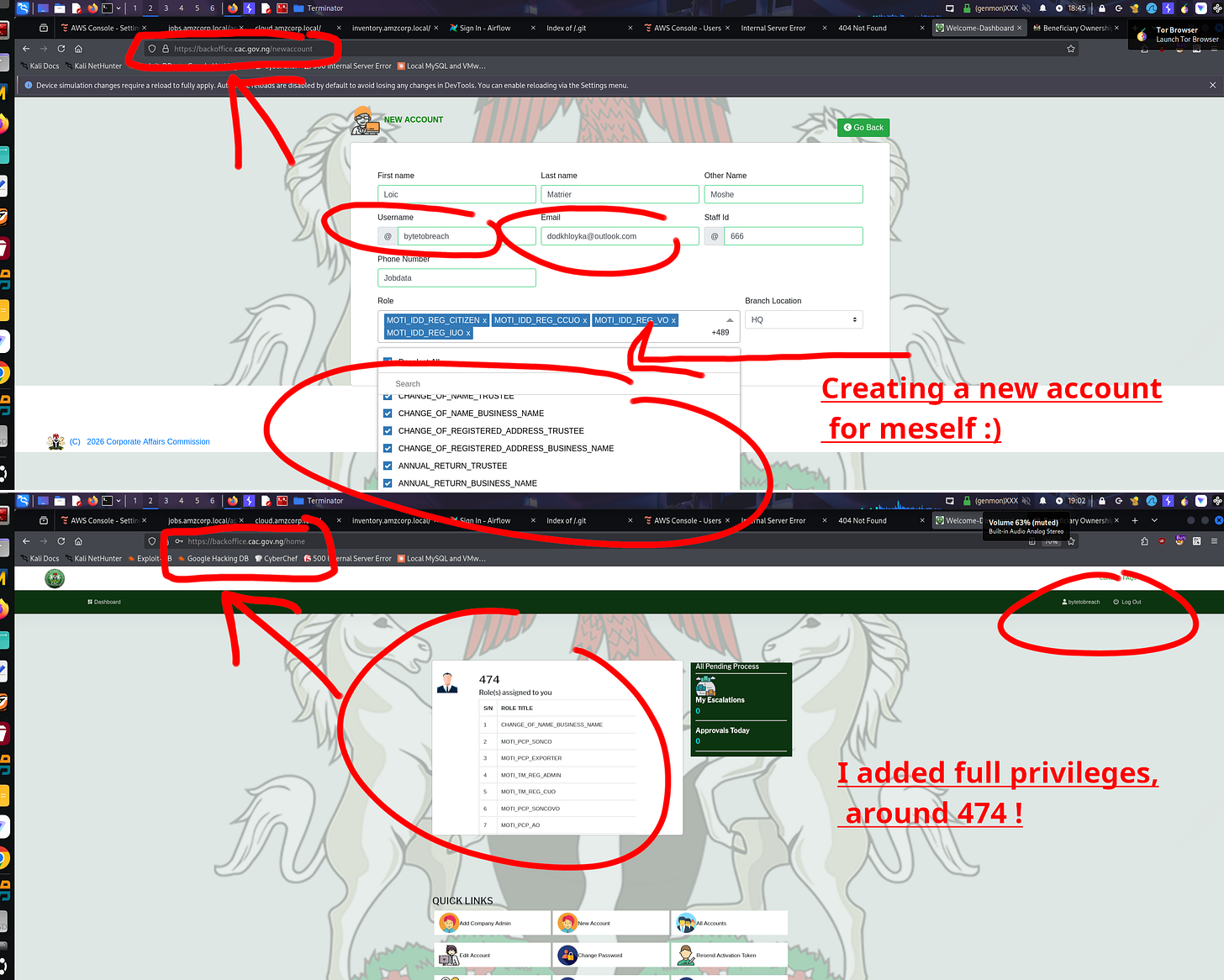
He Gave Himself 474 Roles
Using the authenticated session, the actor navigated to backoffice.cac.gov.ng/newaccount, the panel for creating new staff accounts in the CAC system.
They created an account for themselves.
Username: bytetobreach. Email: dodkhloyka@outlook.com. Staff ID: 666.
Then, from the role assignment interface, they began adding permissions.
They did not add a few roles. They added 474.
The screenshot the actor published shows the dashboard of their newly created account: 474 roles assigned, covering every functional area of the CAC’s back-office system. The actor’s caption: “I added full privileges, around 474.”
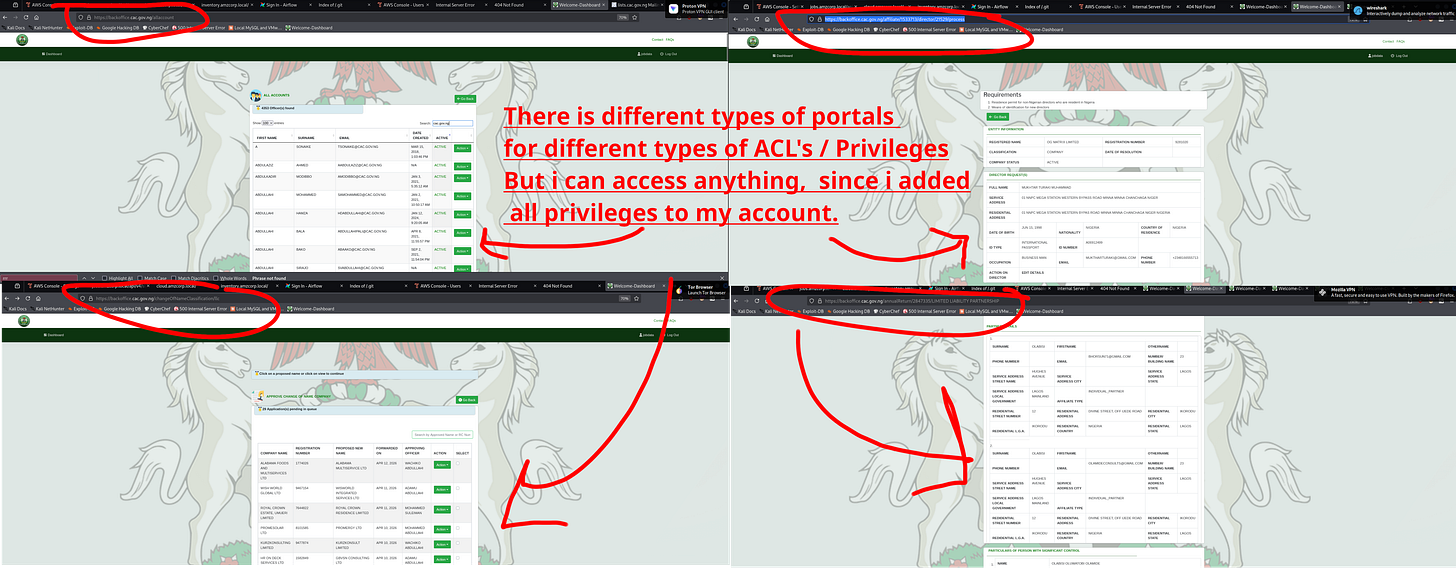
With those 474 roles, ByteToBreach claimed access to every portal in the CAC system. The All Accounts panel, full names and email addresses of CAC staff. The document approval queue with 29 applications pending review at the time of access.
The company search and profile system, full corporate records for any of the millions of registered entities in Nigeria’s corporate registry. Director and shareholder profiles, home addresses, dates of birth, passport numbers, NIN numbers, phone numbers, email addresses. Supporting document archives, passports, affidavits, board resolutions, and notarised documents.
The Scale
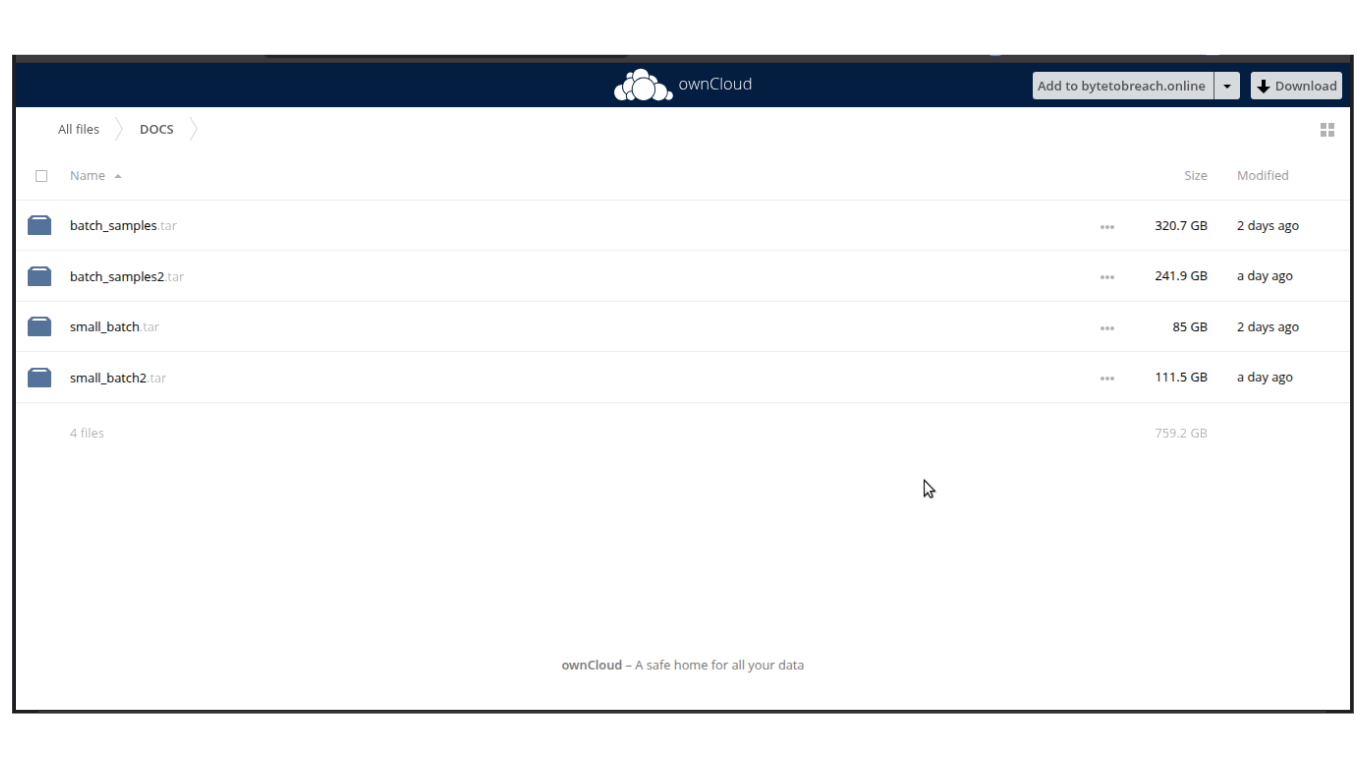
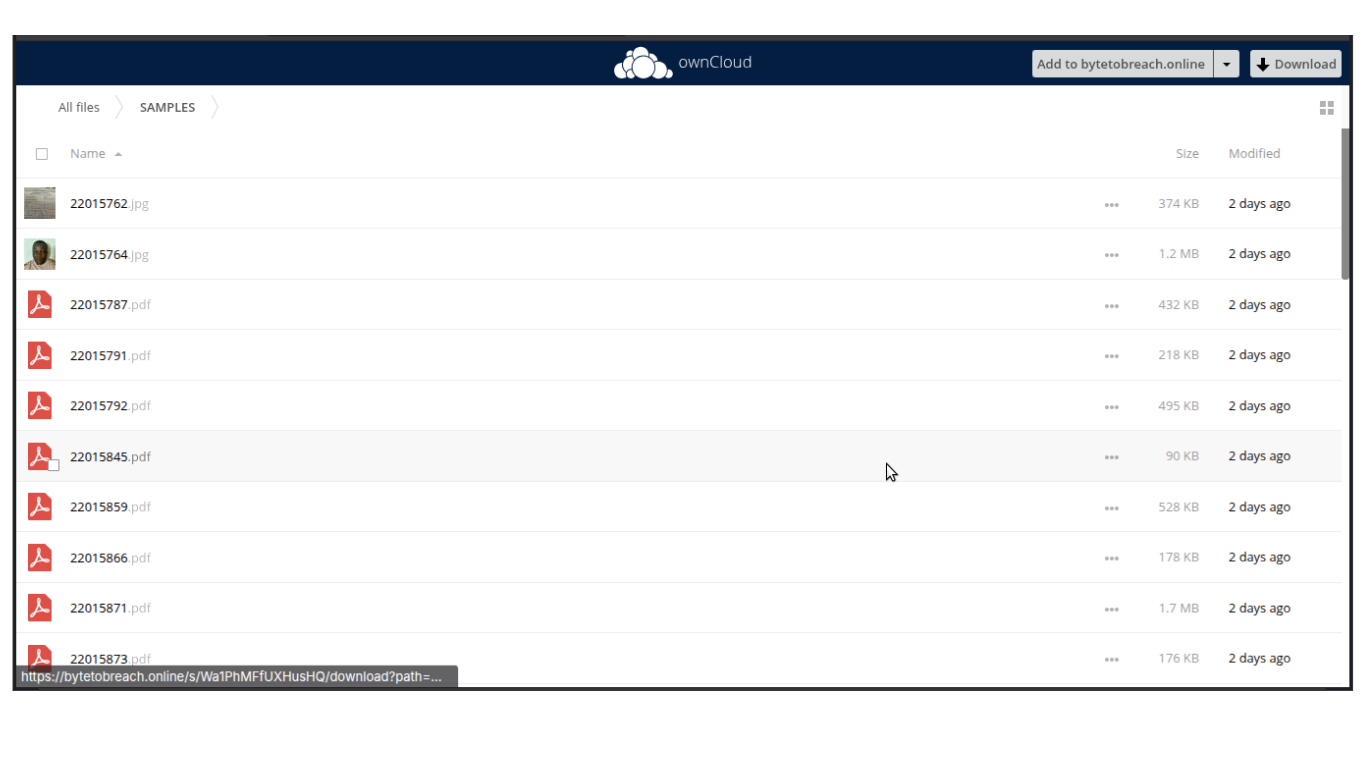
The cybercrime forum post claimed approximately 25 million documents were downloaded from the CAC’s infrastructure. ByteToBreach’s public ownCloud share confirmed a DOCS directory containing four compressed archives totalling 759.2 gigabytes.
The SAMPLES folder contained numbered JPEG and PDF files — individual CAC application records confirming these are real documents from real applications.
When I asked ByteToBreach about the 25 million figure directly, he offered a correction in the direction nobody wanted.
“25 million was the initial assessment. I think the number could be much higher. I didn’t include all the data, due to how big it was.”
The 759GB publicly available for download is not the full dataset. The actual volume of CAC data in his possession exceeds what was published. The true scale of the exposure is not yet known.
The artefacts also confirmed an EMAILS file, 12 kilobytes of plain text containing staff email addresses at @cac.gov.ng in alphabetical sequence.
And two video files. Exfil.mkv and Faster_Exfil.mkv. Screen recordings of the actor conducting the exfiltration. The breach documented on video.
Did He Change Anything
The write access question was the most urgent in this investigation. With 474 administrative roles in the CAC system, the actor had the theoretical capability to modify company ownership records, alter director filings, and change registration information for any entity in Nigeria’s corporate registry.
I asked him directly.
“No records were modified or altered. The only goal is exfiltration and a one-time sale for clients, after failure of extortion.”
No records were changed. The integrity of the CAC registry—as far as this actor’s actions are concerned— is intact. While this is still subject to investigation as it is a threat actor’s words after all, this answer provides some relief to every Nigerian company director and shareholder concerned about their corporate filings.
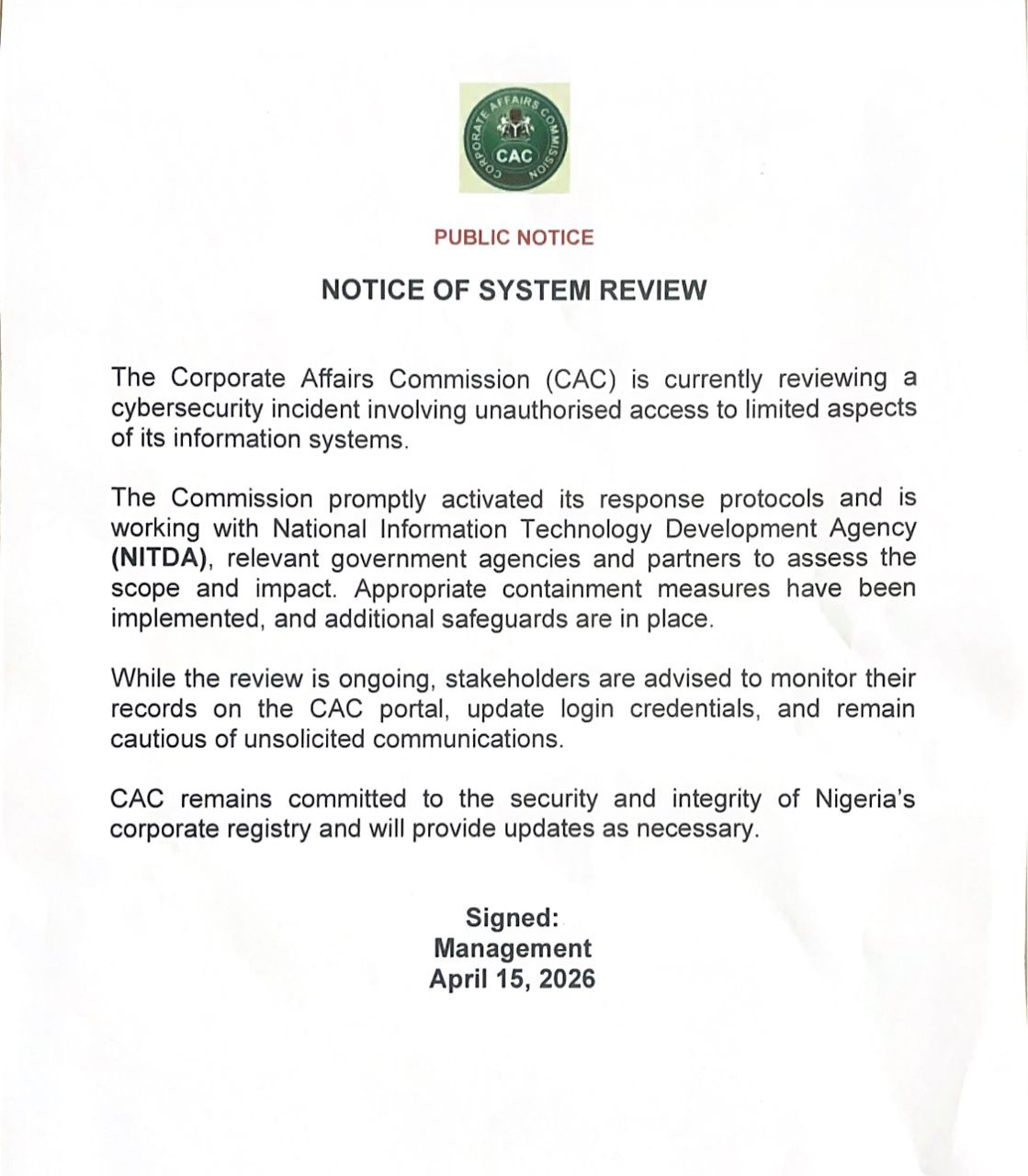
The CAC’s own statement, published the same day, confirmed the agency is reviewing the incident and working with NITDA.
Their advice to stakeholders: monitor records on the CAC portal, update login credentials, and remain cautious of unsolicited communications.
What the CAC statement did not confirm was the scale. “Unauthorised access to limited aspects of its information systems” is the language they chose.
The artefacts show full administrative access across every portal with 474 roles. The actor claims more than 25 million documents. Seven hundred and fifty-nine gigabytes of data are publicly downloadable right now.
The Extortion and the Ransom
I asked ByteToBreach whether he had contacted the affected organisations before publishing.
“All organisations were contacted, and none of them responded, except for Sterling Bank who communicated a possible ransom payment of €250,000, then kept postponing indefinitely.”
All three organisations were contacted before publication. The CAC did not respond. Remita did not respond. Their data was published.
Sterling Bank responded.
Sterling Bank, which has so far refused to comment or issue a single public statement since March 27. Which has not notified its customers. Which was served a Notice of Investigation by the NDPC on April 1, and stayed silent anyway.
Was negotiating a ransom. A quarter of a million euros. Then delays. Then more delays.
The classic crisis management posture. Keep talking, stall, hope the problem goes away. Except the problem did not go away. ByteToBreach published regardless. And hundreds of thousands of Sterling Bank customers spent nearly three weeks unaware that their bank was having this conversation on their behalf.
The NDP Act does not contain a ransom negotiation exemption from the obligation to notify affected individuals. There is no clause permitting a data controller to delay customer notification while conducting back-channel negotiations with the person who has their data.
Why Nigeria
I asked ByteToBreach whether the three Nigerian operations constituted a deliberate campaign against Nigerian infrastructure.
“I guess you can call it a campaign. I usually prefer to reverse malwares or experiment with new technologies in my lab rather than attacking companies, which happens opportunistically and sporadically.”
Opportunistic. Sporadic. Not targeted. Not coordinated. Three doors found open by a threat actor who was looking because looking costs nothing.
He confirmed the CAC operation was independent from Sterling Bank and Remita. And he confirmed that Remita was never a target.
“All access was permitted through Sterling Bank. Were it not for the compromise of Sterling, Remita would never have been hit, since it was never a target to begin with.”
Nigeria’s government payment backbone was not on his list. It was collateral damage from one bank’s decision not to patch a server.
“Protecting Nigerians Is Not My Responsibility”
I asked ByteToBreach about the human consequences. Twenty-five million documents. Ordinary Nigerians who registered companies, filed returns, submitted passports to a government agency and had no say in what happened to them.
“Protecting Nigerians is not my responsibility. That’s the duty of the government.”
He is not entirely wrong about where the duty lies.
I wrote recently about the state of cybersecurity in Nigeria, about the distance between the compliance frameworks Nigerian institutions file and the technical reality of what is actually going on. About a government regulatory model built largely on self-reporting, asking institutions how secure they are rather than verifying whether the answer is true.
ByteToBreach’s four-word answer to my question is the real-world cost of that gap.
The CAC left its system accessible without authentication on a public-facing subdomain. Sterling Bank left a maximum severity CVE unpatched for three months on an internet-facing server. Remita committed production credentials to a Git repository. These are institutional failures. The government, whose duty it is, failed first, not in intent, not in policy, but in the distance between what the frameworks required and what the systems actually did.
His answer about responsibility is technically accurate and morally hollow simultaneously.
The government’s failure to protect does not absolve the actor who exploited that failure and published 25 million citizens’ documents publicly. But it does implicate every institution in that chain, the agencies that left the doors open, the regulators whose frameworks did not catch it, and the bank that knew it had been breached and went silent.
Protecting Nigerians is the duty of the government. The government failed. And nobody — not the hacker, not the bank, not the regulator — told the Nigerians whose information is now in the hands of a global threat actor that any of this had happened.
What Must Happen
The CAC must immediately suspend the JWT generation endpoint, audit all accounts created in the back-office system since April 10, disable or delete the bytetobreach account and any others created without authorisation, review audit logs for every record accessed or modified during the period of access.
NITDA is already involved, according to the CAC statement. Their public assessment of the scope and their recommendations to other government agencies running similar infrastructure should follow.
The NDPC must extend its current investigation to the CAC. The categories of personal data exposed are precisely those the NDP Act's strongest protections apply to.
Sterling Bank must notify its customers. The ransom negotiation does not change that obligation. It makes it more urgent. Their customers deserve to know what was taken, what was negotiated, and what has been done about it.
Every Nigerian institution conducting business against CAC data should treat that data with heightened scrutiny until the CAC confirms registry integrity through its own audit.
The Sign-Off
ByteToBreach ended the response with this.
“You are free to publish anything and on any terms you see fit. I hope I clearly answered your questions. Have a great day, in the grace of the lord.”
A religious blessing. After confirming a ransom negotiation with a Nigerian bank. After noting that protecting Nigerians is not his problem. After acknowledging that the number of documents taken is probably higher than 25 million.
No gloating. No performance. Just a polite, matter-of-fact account of what he did, a permission to publish, and a goodbye.
That normalcy is the most unsettling thing in the entire exchange.
Because the doors he walked through were not hidden. All of them were findable by anyone who cared to look. He looked because he had time.
The question that follows from that is not about ByteToBreach. He has answered for himself.
The question is about the doors. How many are still open? Who else is looking?


"Who else is looking?"
And that's what toeubles me the most.
This is very interesting, teaches us valuable lessons, and should hopefully wake us up.